Centralized control over how your organization uses AI.
Kairro’s policy engine governs both browser activity and collector-backed workstation workflows. Policies combine DLP rules, tool restrictions, domain controls, review actions, and contextual logic into one enforcement layer for real AI usage.
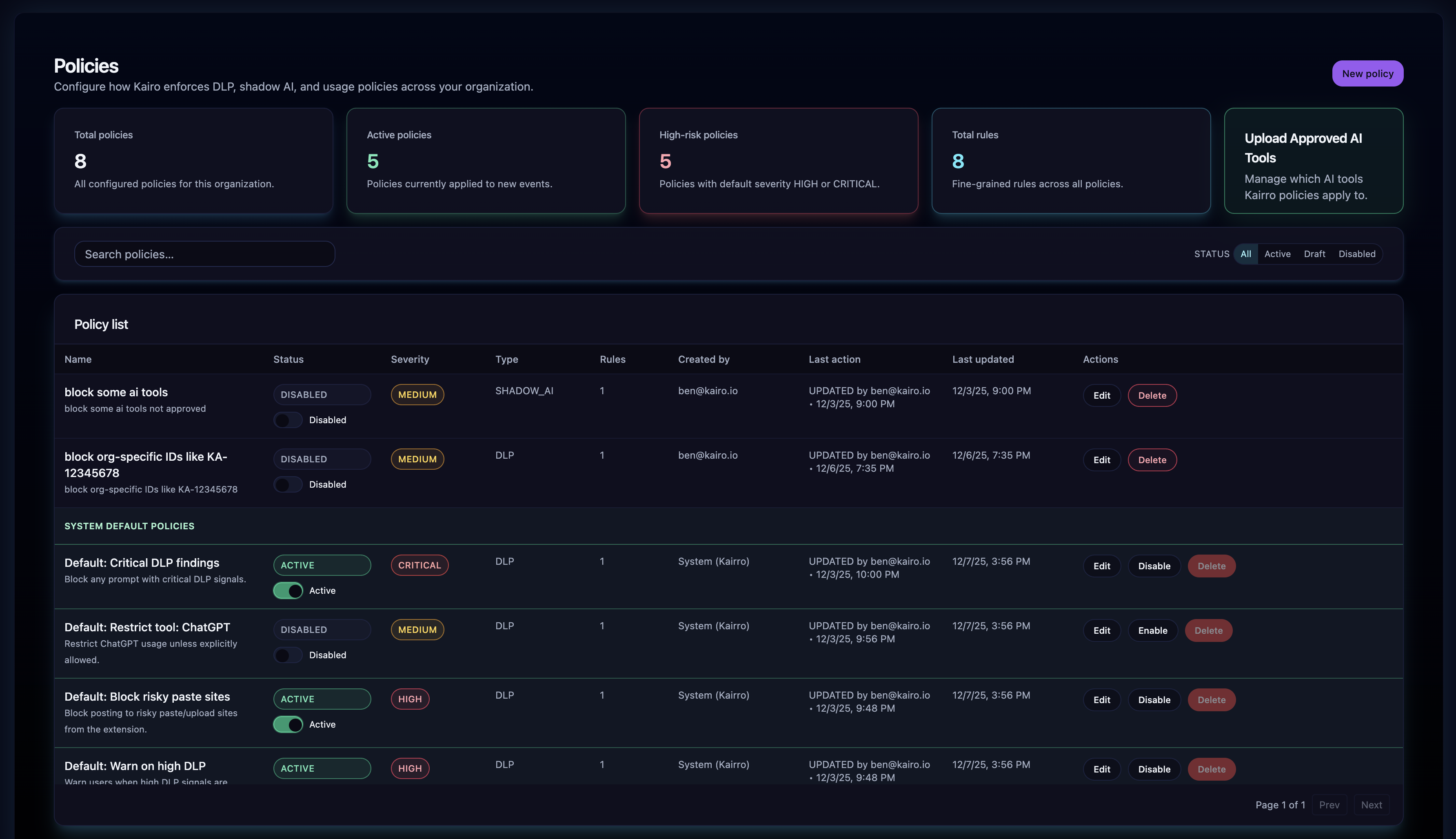
What Policies Control
Define allow, warn, block, and review actions with shared policy logic across browsers and collectors.
Allow, Warn, or Block an AI action.
Org-wide, team-level, or identity-level application.
DLP severity, regex patterns, tools and domains, target surfaces, contextual metadata, and review thresholds.
Generate findings, update investigations, log telemetry, and trigger notifications or downstream integrations.
Policy Model
Core entities that drive real-time AI enforcement.
Type: DLP, SHADOW_AI, ACCESS_CONTROL, OTHER
Status: DRAFT, ACTIVE, DISABLED
Scope: ORG, TEAM, IDENTITY
Priority: lower = earlier evaluation
isDefault: auto-applied by system
Rule kinds: DLP, ALLOW_TOOLS, DENY_TOOLS, DOMAIN_RESTRICTION, TOKEN_LIMIT, OTHER.
Actions: ALLOW, BLOCK, WARN, MASK, ALERT.
Criteria (JSON): minSeverity, regex (prompt/completion/both), allow/deny tools, token threshold, custom matching.
How Policy Evaluation Works
Evaluated with deterministic sequencing across browser prompts and collector-safe policy bundles.
Managed browsers receive approved and unapproved tool definitions; collectors receive signed policy bundles and review-safe rules.
maxSeverity, matches, snippets, totalMatches feed the policy engine.
Org/team/identity policies; ruleMatchesContext; strongest severity wins. Fallback: HIGH/CRITICAL→BLOCK, MEDIUM→WARN, else ALLOW.
Action, risk level, reasons, event ID, DLP summary, and any command sync metadata needed by the client.
Default Policies
Safe baselines for day-one rollout, then customizable rules for real operating needs.
Block on HIGH/CRITICAL DLP
Warn on MEDIUM DLP
Risky domains and tools
Paste sites, unapproved AI tools, and targeted model or domain restrictions.
Targeted review paths
Escalate specific collector-side actions into deterministic review workflows when needed.
Admin Policy Management
Active, Draft, Disabled, Default, Custom.
Add or refine rules, adjust action and severity, target tools or domains, scope by org/team/identity, and publish confidently.
Test policies before rollout, then retain actor, timestamp, and change history for governance traceability.
Policy Delivery to Managed Endpoints
Policies stay centralized, while browsers and collectors receive only the delivery format they need.
Returns approved AI tools, unapproved tool definitions, and version metadata so extensions stay current without exposing unnecessary internals.
Collectors sync signed policy bundles and review instructions so workstation coverage stays aligned with the central policy engine.
Subscription Enforcement & Delivery Guardrails
Managed endpoint coverage, policy delivery, and subscription state all stay aligned.
Valid license required
Active subscription
Endpoint limits enforced
Reliable policy delivery
Browser and collector clients keep policy state synchronized with the admin control plane.
Why Kairro’s Policy Engine Is Different
Evaluates prompt content, model details, identity, DLP matches, tool classification, and token usage.
Prompt-by-prompt enforcement before data is sent; redacted, privacy-safe logging.
Policies interact with DLP, Shadow AI, governance, event telemetry, integrations, notifications.
Clear priorities, structured rules, transparent fallback logic; fully logged for audits.
The Result
Kairro policies let organizations embrace generative AI with confidence.