Real-time protection for sensitive data in AI interactions.
Kairro’s DLP engine brings enterprise-grade data protection directly into browser prompts and managed workstation workflows. Sensitive data detections feed policy decisions, findings, investigations, and governance posture without forcing teams into separate tools.
How Kairro’s DLP Engine Works
A structured pipeline that evaluates prompts and policy-relevant content in real time.
Regex-based detectors
Curated detectors surface structured DLP findings:
- CREDIT_CARD – CRITICAL
- API_KEY_LIKE – CRITICAL
- US_SSN – HIGH
- EMAIL – MEDIUM
- IP_ADDRESS – LOW
Each match: pattern name, severity, snippet offsets, truncated text, rule ID.
Risk signals from matches
- maxSeverity – highest severity
- totalMatches
- highOrAbove – HIGH or CRITICAL
- critical – CRITICAL only
Feeds into the policy engine.
Org-specific rules
Combines DLP severity with policies to produce ALLOW / WARN / BLOCK.
- Scopes: org, team, identity
- Criteria: minSeverity, allow/deny tools, domain restrictions, regex, custom severity/action
Evaluate endpoint returns
- action (allow/warn/block)
- riskLevel
- reasons
- eventId
- DLP summary flags (embedded in the event)
Managed endpoints enforce immediately, while findings and investigations keep the decision traceable.
Why DLP Matters in AI Workflows
Generative AI can unintentionally leak sensitive data. Kairro helps stop exposure across browser and workstation-driven AI workflows.
Customer PII & regulated IDs
Credentials / keys
Internal documents & source
Proprietary logic
DLP Events & Logging
Stored in Event with identity, AI tool, action, redacted prompt/response, DLP flags, tokens, metadata.
Stored in DlpMatch with patternName, severity, offsets, ruleId, detector type (REGEX), linked to the event.
Prompts/responses/snippets truncated to 256 chars; offsets/metadata only; logging detail configurable per org (eventsLoggingLevels).
Default DLP Behaviors
Safe-by-default enforcement via ensureDefaultPolicies.
HIGH / CRITICAL
Hard block on high-severity detections out of the box.
MEDIUM
Guided warnings to keep users productive while reducing risk.
High-risk channels
Paste sites, unapproved AI tools, high-risk providers, optional ChatGPT deny—ready on day one.
Org-Level DLP Tuning
- Severity thresholds (e.g., “Block on MEDIUM+”)
- Custom regex detectors
- Target: prompt / response / both
- Allow/deny tools by severity
- Scope: org, team, identity
- Prevent full document uploads
- Block sensitive API keys
- Enforce PCI/PII controls
- Warn on customer names/emails
- Higher risk tolerance for specific teams
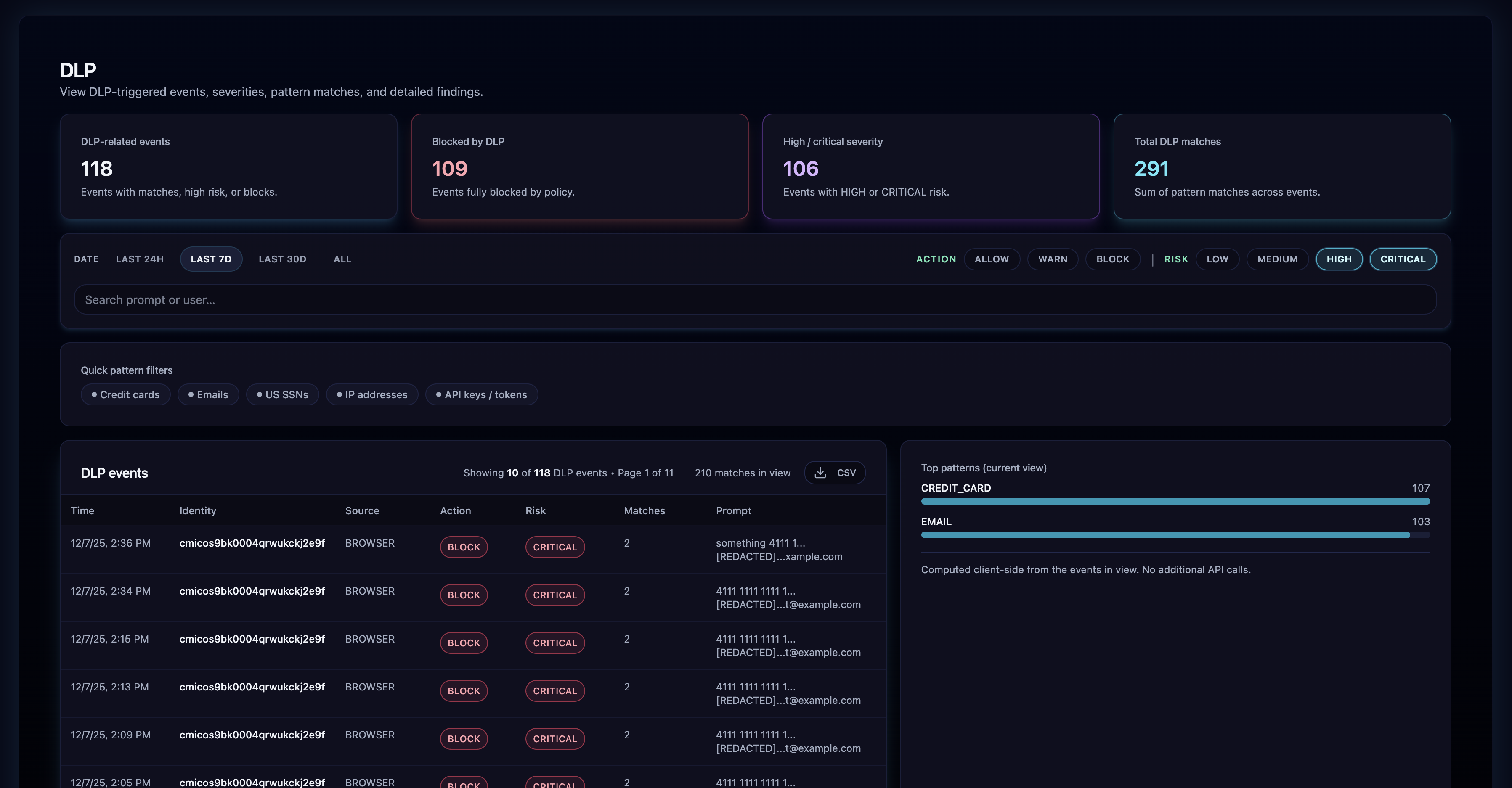
DLP Analytics in the Admin UI
Per-event: isDlpEvent, blockedByDlp, maxSeverity, highOrAbove, critical, totalMatches.
/v1/admin/events/:id/dlp returns full match list, patterns, severities, redacted snippets.
DLP counts, high/critical last 7 days, top patterns (up to 20), block/warn ratios, trends. Capped scans (~5000 events) for consistent performance.
DLP in Real-Time Workflows
Extension enforces at the moment of use; all decisions are logged with traceable metadata.
If block threshold met
Prompt is blocked.
If warn threshold met
User receives a warning UI.
If allowed
Prompt continues.
Why Kairro’s DLP Is Different
Purpose-built for AI
Prompt-level focus, structured snippet metadata, real-time evaluation, integrated with policy/governance.
Designed for Shadow AI
DLP fires even on unapproved tools; events enter the Shadow AI pipeline.
Enterprise-safe by design
Redacted logging, scoped policies, full audit logs, and SIEM/SOAR/incident workflow integration.
The Result
Kairro’s DLP gives organizations confidence to allow AI adoption safely.